There are many browsers available to us. We have many types for both desktop and mobile devices. Some, as we know, are more based on privacy and security. Today we are going to talk about which browsers we can find to enter the Dark Web anonymously and privately. We can make use of different options, as we are going to see.
Browsers to enter the Dark Web
If we talk about the most popular and used browsers, Google Chrome, Mozilla Firefox or even Edge probably come to mind. But there are many more. Some of them have a very small market share, but they may have very different features from the most popular cases.
When surfing the net, we can use any browser. It is clear that this is its main function. But if we talk about browsers that allow us to enter the Dark Web or surf anonymously, the number is reduced. They can also help to improve security and avoid certain problems that can damage the operation of our computers.
Tor Browser
Undoubtedly, one of the most popular browsers for accessing the Deep Web is Tor. In fact, it was the first browser that came out for this purpose. Moreover, it is totally based on privacy and security. It is even today one of the preferred options for those looking for an alternative to the most popular ones.
The Tor browser allows you to browse the Deep Web. It is available for most operating systems such as Windows, macOS, Linux or Android. It can help us to improve privacy on the network. This is independent of whether we can enter the Deep Web. We can use it on desktop computers and also on mobile devices completely free of charge.
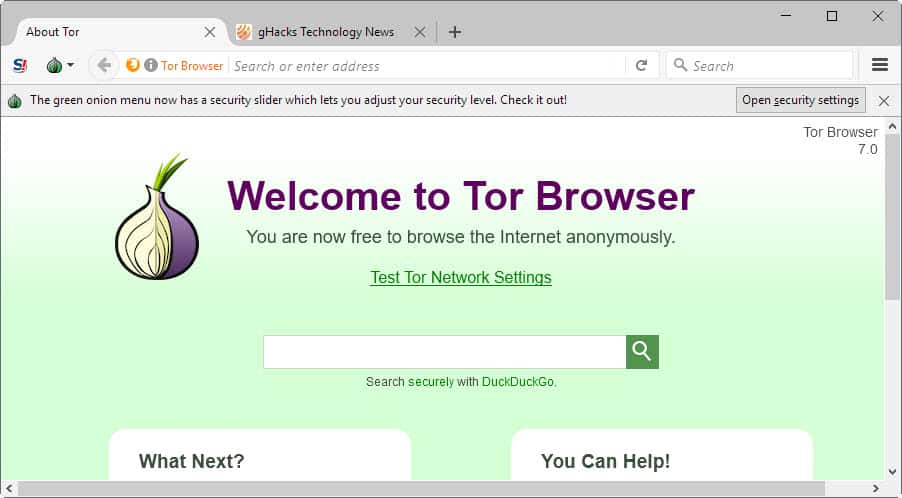
We can download the Tor browser from its official website. There we will find the different versions available. As we always say, we recommend downloading this type of programs from reliable sources.
Subgraph
Another option we found is Subgraph. This is an open source browser that allows you to enter the Dark Web. It is based on Tor, but in this case we are dealing with an operating system and not just a browser.

It has a very restrictive privacy policy. This means that many users rely on this tool to surf the web when they are looking for maximum security. It has a file encryption system and even comes with an instant messaging program. You can find all the information on its web page.
I2P
There is also the I2P alternative. It also works through layers to achieve private and secure browsing. It is based on a tunnel system so that data can travel without being intercepted. A way to encrypt that information and prevent it from ending up in the hands of third parties that could harm our privacy.

Both the sending and receiving clients will use a tunnel. In this way, messages can be sent and received fully encrypted. In addition, there is no possibility that the information can be filtered. It acts, in a way, as a VPN. In short, I2P is an interesting option if you are looking for anonymity on the network. More information can be found on their website.
Whonix
A more unknown option is Whonix. It is a browser that is available for Windows, macOS, and also Linux. It allows us to surf the web anonymously. Once again, this is an option based on the Tor browser. It has a system that prevents our IP address from being exposed when browsing. This is achieved by using a virtual machine. This should be noted. In effect, it is part of an operating system rather than a standalone browser. A different alternative to others we have shown previously.

Another very interesting thing about this browser is that it also has its own operating system, based on anonymity. This is formed by two virtual machines, where one of them is dedicated to run a Tor proxy, which does the function of gateway. And the other virtual machine is called Whonix-Station, which is located in an isolated network. It is a simple system to install if you have slight knowledge about Linux or this type of system.
Advantages and disadvantages
This brings some benefits. The most striking is that it will be extremely difficult for an attacker to know our IP. Indeed, all incoming and outgoing connections go through the Tor network. This also includes applications that do not support the proxy. In this case, it is done by Firewall. This also protects us against root exploits. But in the event that one manages to infect our computer, the system itself ensures that it does not affect the integrity of the processes.
Whonix can be used with a VPN or SSH connection, as all serial numbers will be hidden. This includes the computer where the Virtual Box is running, or the virtualization service we use. At the same time, this operating system has some disadvantages. To go further, it is very slow to perform updates. In addition, it requires a lot of resources on the computer to work properly, this in terms of CPU and RAM. Logically, since the computer will be running two virtual machines instead of one as usual. But on the other hand, we have all the advantages offered by Linux-based operating systems. For example, the apt-get packaging tool, which allows us to install all kinds of new tools.
Tails
Like the vast majority of dark/deep web browsers out there, the Tails darknet browser is again based on the original Tor browser. However, this build could be better defined as a live operating system. Especially since it can be booted and accessed from a USB stick or DVD without installation.
This then relies on the use of highly advanced cryptographic tools to add the protective layers that ensure you remain hidden as you browse the Internet. This includes all files, messages, videos, images, and emails sent and received by you and your accounts. To maximize the level of security you have while browsing, Tails Onion Browser Dark Web will automatically shut down and temporarily stop the use of any operating system you are currently using. This really minimizes the risks of being discovered.
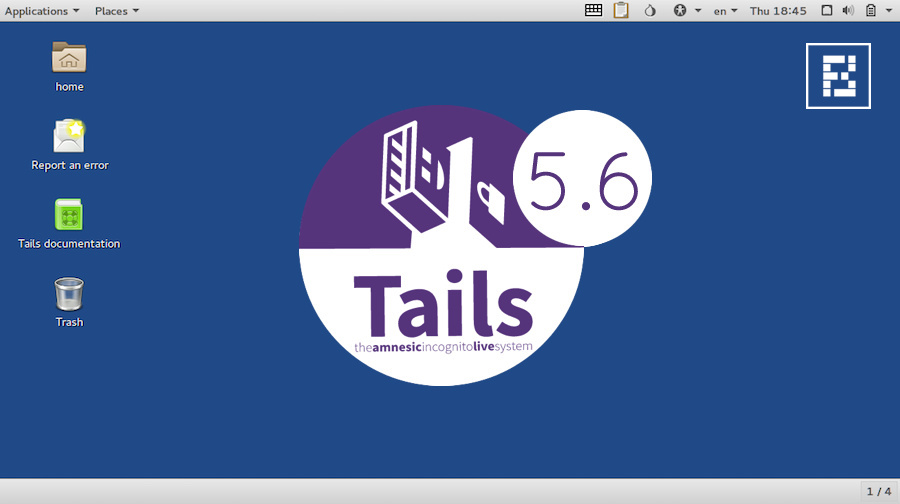
Of course, all of this will return to normal once the Tails system has been shut down. Don’t worry, only RAM is used to run this operating system, and the hard drive and disk space will remain intact. While Tor may be the most popular hidden web browser, the Tails operating system is, in fact, one of the best.



